NaibofTabr
- 0 Posts
- 211 Comments

 71·8 days ago
71·8 days agoOr just reinstalls it in the next update.

 21·8 days ago
21·8 days agoI’m having trouble understanding your point. What is the “quiet part”? That representatives from a foreign government visited Taipei?
You’re welcome. I tried to do basically the same thing a few years back (run a WordPress site from a RPi on my home network - and also a Minecraft server) and so I tried to write up the problems I ran into - I probably forgot some, but those are the major hurdles. I learned a lot along the way.
I should also point out that if you rent hosting space (from linode or inmotion or digitalocean or many other options) then problems 1 & 4 become much easier, and 2 & 3 go away entirely (most people don’t host public websites on their home networks because of these and other issues).
Happy to help. If you’re interested in learning networking more thoroughly, I want to point you to Professor Messer especially the Network+ content. He has far more complete explanations than I could write (and it’s free!). Even if you’re not interested in getting any certs, the explanations will be helpful.
So your goal is to host a publicly accessible static website from a computer in your home. There are a few problems you need to overcome before even worrying about configuring any software. You need some more basic networking knowledge first.
-
Basic Networking Theory - you should read a brief explanation of the OSI 7-layer network model. You don’t have to try to memorize this and you won’t really understand it until you start actually doing stuff, but you should read it for some basic terminology and to understand that there are distinct steps through which communication between computers happens.
When you start running into problems (“why can’t I access the server? I did all the tutorial steps”), figuring out which layer the problem is in will help guide you to the solution:
- is there a bad cable? -> 1. Physical
- do I have the right IP address? -> 3. Network
- is the firewall port closed? -> 4. Transport
-
Privacy/Security/Safety - don’t host a publicly accessible website from your personal computer. Just don’t. To make this happen you will have to open a hole in your network security that makes your computer accessible from the public internet. Don’t do this on your daily driver computer. Don’t do this with any device that has any files on it that you care about or any access to any personal information. Don’t.
Set up your web server/learning environment on a clean, dedicated system. This could be an old laptop or a Raspberry Pi (an older 3B model will work just fine for this) or whatever cheap computer hardware you have, as long as it can run Linux and has a physical network port (using WiFi will give you extra headaches for getting this working). If you think you might want to expand your projects in the future, you can get a used Dell server for very little money, and add more hard drives as needed. Wipe the hard drive and install Debian or Ubuntu server as a base, there’s lots of resources out there for setting up web services on either.
-
Restricted Ports - you are most likely on a residential internet connection. Most residential ISPs close ports for security reasons, especially 80. For example, here is Cox’s list of restricted ports. You will need to find your ISP’s equivalent list and understand what you can and can’t do with your connection.
There are workarounds, primarily through port forwarding. You will need admin access to your router to set this up. I recommend that you read that entire article because it probably applies directly to your situation.
-
Dynamic IP Address - most people still find it easier to work with IPv4 addresses - I won’t go into IPv6 right now, but you should read a little about it just for awareness. Your residential internet most likely has a dynamic IPv4 address, which means you can’t rely on that address staying the same forever (or even until next week), which means that you can’t configure your Cloudflare domain name to point to a single IPv4 address.
Dynamic DNS is the solution for this, and again you’ll need admin access to your router to set it up.
-
HTTPS/TLS/SSL - if you get through all those issues then you probably have a working website, but now you’re seeing something like this when you try to view it in your browser:
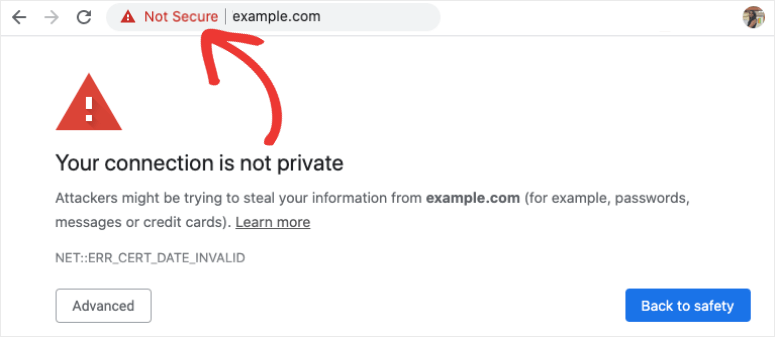
This doesn’t mean that you can’t get to your website - it just means that you can only do it via HTTP and not HTTPS, which the browser is warning you (and anyone else trying to view your website) is not secure. You can either just accept that this alert will always come up, and that you have to click through it, or you can learn about TLS and getting an SSL/TLS certificate. This is a later topic - it doesn’t matter and probably won’t make sense until after you’ve got your web server online.
-

 3·12 days ago
3·12 days agoWhat are your interests like? Do you want to do engineering-type stuff in your personal time, or not-work-related stuff?
Do you have a separate room from your bedroom, or is it a studio? Some projects are small enough for an apartment, but you don’t want to sleep with them (anything involving harsh chemicals or hot plastic).
Do you have space for a dedicated workbench/desk? One thing that really helps with my own projects is having space to leave them out while they’re in progress. Having to pack them up and then unpack them again is a real hassle.
Do you have a balcony/patio/outdoor space?
Is money a consideration? Some projects have a high barrier-to-entry (a usable 3D printer will cost several hundred dollars up front).
Possibly most important, do you have any ideas that you want to create but aren’t sure how to get there? Projects are most successful when you have a vision for what you want to do, and the skills and tools you pick up along the way are just a means to an end.

 5·16 days ago
5·16 days agoAlternatively, Material Files (available in F-Droid) can easily create a local FTP server or connect to a NAS. It’s also a pretty good file manager app.

 7·18 days ago
7·18 days agoI think you’d also like NakeyJakey’s game design essays and infernoplus on halo modding.
Thank you for sharing your playlists!
Yup, and it might be necessary to reproduce a lot of the answers that people used to find on reddit.

 22·21 days ago
22·21 days agoSee also: BOFH
China won’t play along. All time is the same time in China.
a local solar time for the things that do not matter and an official or coordinated time?
We basically have this already in the form of UTC+0 (GMT). For most cases where organizations need to coordinate operations across time zones, they just have everyone use GMT.
It’s not so much advocating this situation as it is pointing out that it’s the system we’re living under.
This is not a valid interpretation, because the wolf is wearing a jacket with the anarchy symbol in the last frame, in which it advocates for the use of direct violence to seize property. Also, the frame before this says:
“The wolf devoured him on the spot, and redistributed his property among the wolf pack.”
This is a sort of benevolent strong-man fantasy, where the mighty (violent killers) redistribute wealth (in a presumably equitable way?) because they are willing and able to exert force to do so. It wants to paint itself with the Robin Hood mythology (rob the rich and give to the poor) but it is actually a disgusting fetishization of violence as a source of moral superiority.
In fact, there’s no reason why we should consider the wolf to be any more moral than the pig, as their story begins with property destruction (unprovoked, so far as we know in this context) and then moves on to murder and theft. The benevolence or charity they might perform after these actions does not excuse or redeem the destruction, murder or theft. Based on what is presented in this comic, the wolf is demonstrably a less moral individual than the pig. This isn’t even ambiguous, because they didn’t actually bother having a conversation with the pig - they leapt straight to murder as a solution to what they perceived to be a problem.
Perhaps the wolf is a valid representation of anarchist ideology. If so, anarchists need to reexamine their ideology.
Um, I think this is literally advocating “might makes right”.

 38·26 days ago
38·26 days agoOof, blaming the victim.

 13·27 days ago
13·27 days agoPowerPoint is ridiculously capable, like to an unnecessary degree.

 11·1 month ago
11·1 month agoI would guess it’s the lower fridge in case the items are supposed to be falling and the fridge will be the first one to hit the floor.
wut.

 2·1 month ago
2·1 month agoSome explorations for you: (steam links for reference, but I recommend going into all of these blind, don’t read a lot of reviews)
Agile development.



Believe it or not, I can be concerned about both.
The difference is, the place where I live has some data privacy regulations which actually get enforced, and I have some legal recourse against organizations which mishandle my data. China does not have such regulations and I do not have any recourse against organizations based there, so my risk from them is significantly higher.